Insights
Insights & updates
Explore the latest trends, expert guidance, and actionable insights in IT cybersecurity. Filter content by topics that matter most to your business.
Technical Webinar: How to Maximize Your Microsoft Secure Score
Join us as we dive into Microsoft Secure Score and how it can help you strengthe...
Is your Microsoft environment protected from Storm-2372
Are you protecting the core of your business operations from Storm-2372? In case...

How to Help Prevent Vendor Fraud
It’s 2025, businesses are all online, their vendors are all online, and they are...
Tutorial: SCuBA Your Microsoft 365
Introduction Managing security and compliance in Microsoft 365 (O365) is crucial...
Technical Webinar: SCuBA Your Microsoft 365
This webinar is all about SCuBA. A powerful security scanning and assessment sol...
How to Use Microsoft Secure Score to Build a Long-Term Security Roadmap
You’ve raised your Microsoft Secure Score and aligned it with NIST CSF in our pr...
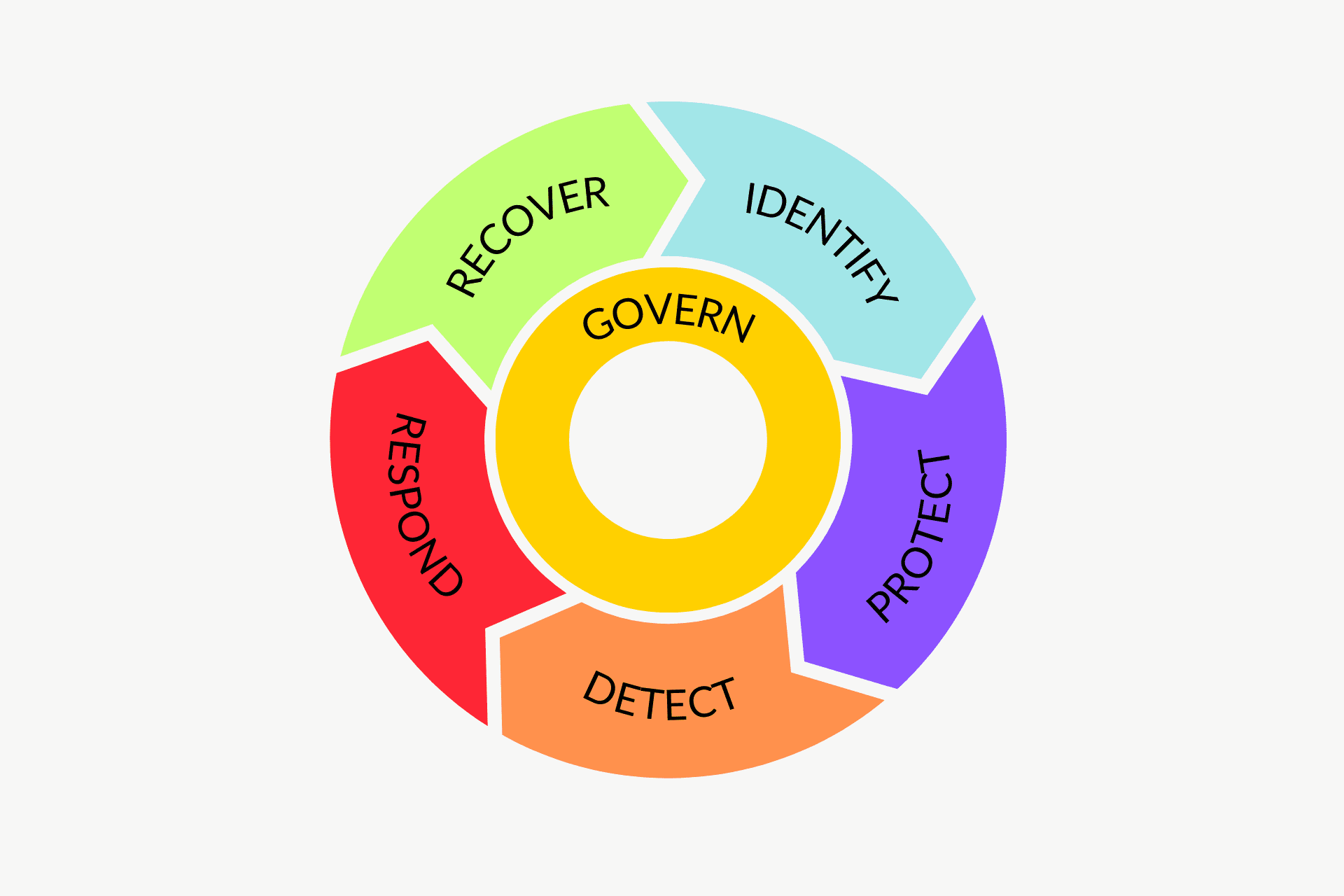
Aligning Microsoft Secure Score with Industry Standards: A Guide to NIST CSF
We showed you quick wins to boost Microsoft Secure Score in our previous post. B...

Top 5 Microsoft Secure Score Recommendations for Immediate Impact
We’ve covered what Microsoft Secure Score is and why it’s crucial. Now, let’s ge...

What Is Microsoft Secure Score and Why Should You Use It
If you’re looking for the key to enhancing your organization’s Microsoft 365 sec...
Strengthening Your Microsoft 365 Security: An Enterprise Guide for 2025
Did you make a New Year’s resolution this year? If so, you’re not alone. Lots of...
Navigating Cybersecurity Leadership: Tips for Finding the Right vCISO for Your Organization
In early October, hackers targeted American Water, one of the largest utility pr...
The Anatomy of a Cyber Attack: Lessons from the Front Lines
Here’s a quick story that will send shivers down the spine of every CEO.

The Role of Penetration Testing in Protecting Your Organization
What is Penetration Testing? Businesses can no longer afford to take cybersecuri...
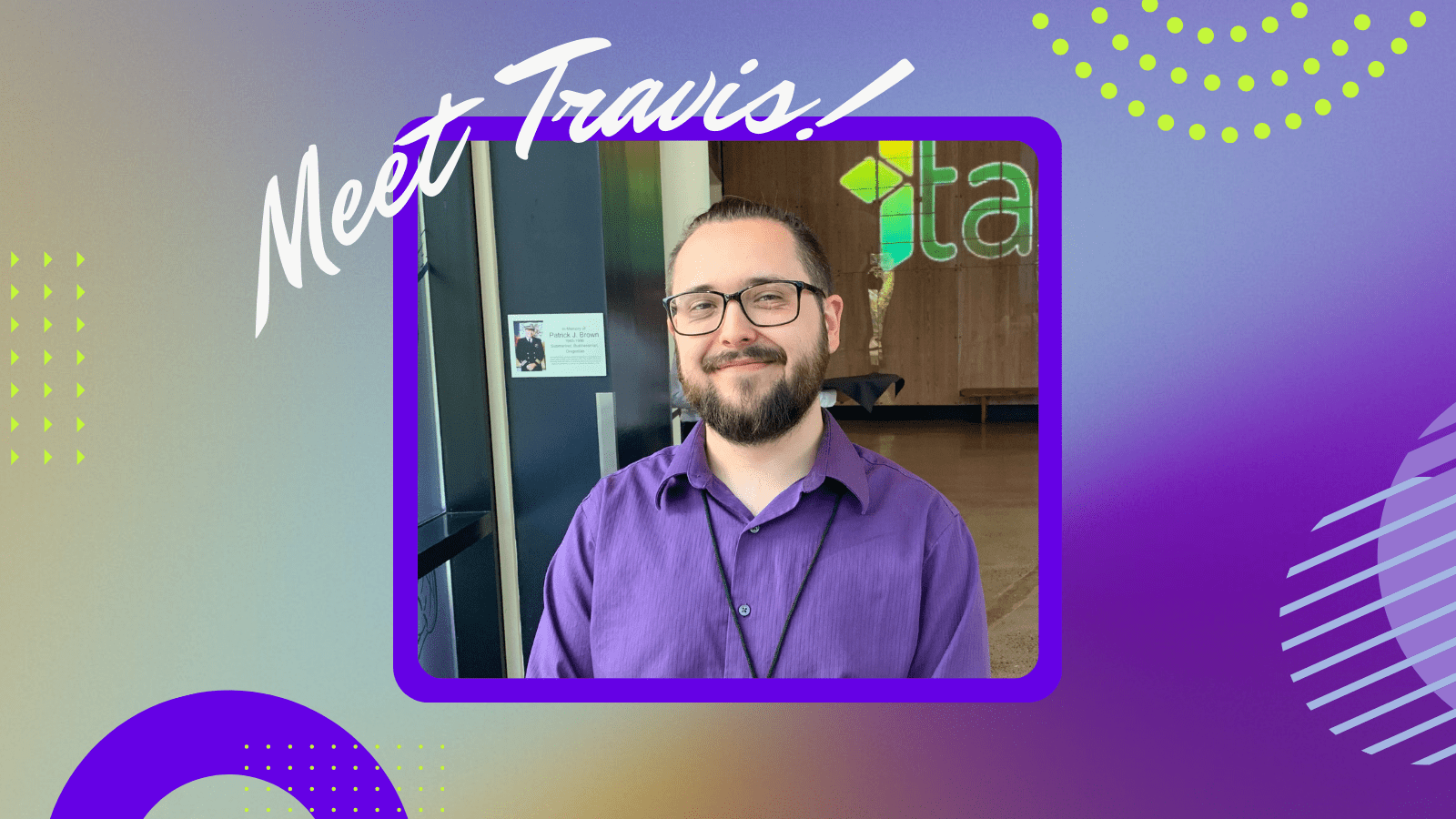
Meet Travis: edgefi’s Tech Team Lead
Our goal at edgefi is to help our customers build security operations that evolv...

The Story Behind Edge Networks’ Rebrand to edgefi
The Story Behind Edge Networks’ Rebrand to edgefi We’re thrilled to have entered...
Meet Megan: edgefi Welcomes a New Project Coordinator
With all the exciting news in the last few weeks, we’re excited to share that we...

Cybersecurity Firm Edge Networks Rebrands After 18 Year History
Innovative Cybersecurity Firm Edge Networks Rebrands as edgefi After 18-Year His...
edgefi Wins Emerging Award at the 40th Annual Oregon Tech Awards
edgefi (formally Edge Networks) Wins “Emerging Award” at Oregon Tech Awards Port...

Sip and Secure: May Happy Hour Recap
Sip and Secure Recap Last week, our local cybersecurity community gathered at th...
Meet Noah: Edge Welcomes a New Help Desk Analyst
We’re excited to share that Edge Networks is growing! This has been propelled no...

Edge Networks: Celebrating Our Nomination for the Technology Company of the Year Award
Edge Networks Announced as a Finalist for Emerging Company of the Year by Techno...

Understanding Identity Theft: Strategies to Secure You and Your Organization
The Rise of Identity Theft Online transactions offer convenience, but they also ...

Meet Michael: Edge Networks Welcomes a New CISO
At Edge, our journey since 2006 has been about more than just growth—it’s been a...

The Evolution of GRC (Governance, Risk, and Compliance)
The Evolution of GRC: From Check-the-Box to Strategic Asset In a 2023 report by ...

How to Remediate the Cybersecurity Leadership & Strategy Resource Pain Through a vCISO Program
Mission Possible: How to Remediate the Cybersecurity Leadership & Strategy R...

Sip and Secure: January Happy Hour Recap
Sip and Secure Recap Last week, we had the pleasure of hosting our Sip and Secur...

The Essential Guide to Vulnerability Management
Vulnerability Management Working Behind the Scenes Cybersecurity is riddled with...
Why You Should Focus Your Q1 Activities on the “Identify” NIST CSF Category
Why You Should Focus Your Q1 Activities on the “Identify” NIST CSF Category “You...

Top Cybersecurity Trends in 2024 to Look Out For
Uncovering the Top Cybersecurity Trends in 2024 As we welcome a new year, it’s e...
Exposing Lockbit 3.0: A Proactive Guide to Defense Strategies
LockBit 3.0: Navigating a New Frontier in Cyber Threats When it comes to the lat...
Edge Networks Honored as a Top 10% Clutch Champion for 2023
Edge Networks Honored as a Top 10% Clutch Champion for 2023 Edge Networks has be...

The CISO’s Guide to Cybersecurity Maturity
The Journey to Cybersecurity Maturity From executive boardrooms to the heart of ...
Edge Networks Named 2023 Global Award Winner by Clutch
Edge Networks Named 2023 Global Award Winner for Cybersecurity Services by Clutc...

15 Steps to Align Your Cybersecurity Program with Your Company Mission
Mission Possible: How Cybersecurity Can Align with Your Company’s Mission Improv...

Cyber and Cider 2023 Event Recap
The History of Cyber and Cider In October 2022, Edge Networks kicked off its fir...

Edge Networks Wins UpCity’s Best of Washington 2023 Award
Edge Networks Wins UpCity’s Best of Washington 2023 Award We are thrilled to ann...

6 Ways to Protect Your Organization from Business Identity Theft
What is Business Identity Theft?

The Human Element: Building a Strong Cybersecurity Culture
The Human Element in Cybersecurity When it comes to cybersecurity, we often focu...

Navigating Cybersecurity Compliance: A Comprehensive Guide
Understanding Cybersecurity Compliance: Safeguarding Your Business Against Digit...

Future Leaders Project: Thomas’ Cybersecurity Internship at Edge
The Future Leaders Project The Future Leaders Project is an initiative of Workfo...

A Deep Dive into the Recent Casino Cyber Attacks
A Deep Dive into the Recent Casino Cyber Attacks and How to Be Proactive in Your...
Future Leaders Project: Johnny’s Marketing Internship at Edge
Workforce Southwest Washington’s Future Leaders Project The Future Leaders Proje...

What is a Cybersecurity Assessment?
Building a Secure Digital Environment with Cybersecurity Assessments Imagine fin...

Cyber Insurance Checklist: What to Expect When Applying
Cyber Insurance Checklist: Questions to Expect When Applying The threat of cyber...
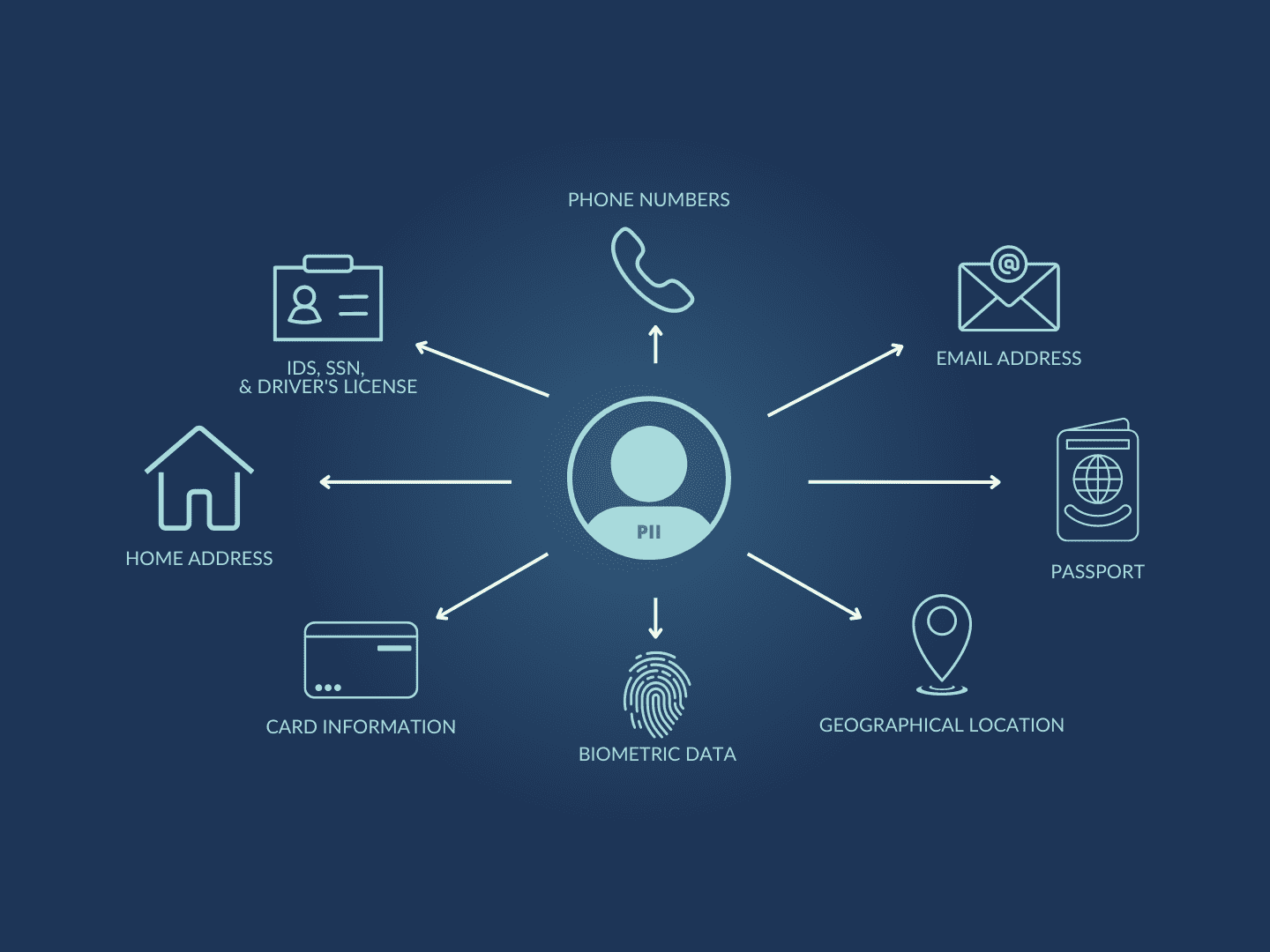
5 Tips for Protecting Personally Identifiable Information (PII)
Protecting Personally Identifiable Information (PII) One thing is clear: protect...

Public WiFi Security Tips: Always Use a VPN and Anti-Malware
The Ups and Downs of Public WiFi Picture this: You’re at your go-to café, sippin...
A Guide to Vendor Impersonation Fraud
Protecting Yourself in the Digital World In today’s interconnected digital lands...
3 Steps to Secure Your Company with a Password Manager
Why is a Password Manager so Critical? The average person has 70 to 80 passwords...
Passkeys: The Future of Password Security
Passkeys: The Future of Passwords When it comes to digital security, passwords h...

Ask an Expert: History Repeated with Another T-Mobile Data Breach
Ask an Expert: History Repeated with Another T-Mobile Data Breach T-Mobile has b...
3 Skills You Need to Get Hired in Cybersecurity
In light of the recent wave of layoffs, we want to provide as much information a...
The Top 3 Cybersecurity KPIs Every Business Needs to Track
Key Performance Indicators (KPIs) are an excellent way to measure your team’s su...
Tips for Safer Internet Day 2023
Tuesday, February 7th, 2023 is the 20th anniversary of Safer Internet Day! The m...
Cybersecurity Trends To Follow Beyond 2022
As the digital world continues to grow, so does the cyber threat landscape. Ther...
5 Reasons Outsourcing Your IT Is a Smart Business Decision
In today’s world, businesses need to be able to rely on their technology. When s...
Cyber and Cider 2022 Event Recap: A Happy Hour for Local Professionals
The Event In November, Edge Networks held a happy hour for local professionals, ...
Smart Home Breaches: How to Prevent Them and What to Do If They Happen
It’s no secret that smart homes are becoming more and more popular. For many, a ...
Spyware: The Silent Threat to Your Business
Are you the first line of defense for your business? Do you know what’s going on...
The Importance of Protecting Your Sensitive Information in 2022
As more and more people get on the internet and start sharing information, data ...
Human Error in Cybersecurity Breaches
Running a business is difficult work. There are so many factors you need to cons...
AUGUST 2022: Major Vulnerabilities Found on Apple Devices, Users Urged to Update Software
On Wednesday, August 17th, 2022, Apple released two security reports revealing s...
4 Ways Penetration Testing Can Improve Your IT
You’ve probably heard of penetration testing, but you may not be entirely sure w...
How to Choose the Right VPN Service For Your Business
Your location, IP address, browsing history, and device type are some of the thi...
Everything You Should Know About Password Managers
47% of American adults have had their personal information exposed by cybercrimi...
Cybersecurity: What Is It And Why It’s Important For Your Small Business
Cybersecurity: What Is It And Why It’s Important For Your Small Business
Edge Networks Ranked #1 in Cybersecurity & IT Firms in Washington
Since 2006, Edge Networks has been providing all-things IT to our clients in ord...
Why You Should Be Using Multi-Factor Authentication (MFA)
Data breaches are at an all-time high. If you’re one of the 56 percent of intern...

How a Managed IT Service Provider Can Help You Avoid Social Engineering Attacks
A cyber attack on your company could cost you millions of dollars and cause you ...
Server and Network Management Basics
When you set up your own business, the details of the network and servers might ...
5 Reasons Your Business Needs an Incident Response Plan (+ Free Template!)
Did you know that Americans face a hacker attack every 39 seconds, and 43% of th...
How Your Business Can Save Money by Outsourcing Managed IT
Save Money by Outsourcing Managed IT Running a business in today’s fast-paced la...
6 Tips For Implementing New Technology In Your Business
6 Tips For Implementing New Technology In Your Business
Everything You Should Know About Backing Up Your Data
The essential way to store your information
What do Virtually All Phishing Attacks Have in Common?
How to figure out if an email is genuine or “phish-y”
The Differences Between Data Loss, Data Leak, and Data Breach
The Differences Between Data Loss, Data Leak, and Data Breach
7 Cybersecurity Tips for Small/Medium Businesses
Cybersecurity Tips for Small and Medium Businesses If you run an SMB (a small or...
Do You Know the True Cost of Data Loss?
You Lose More Than Data with Data Loss
Cybersecurity Strategy Series Episode 1: Proactive Technologies
Which Security Solutions Does Your Business Need? It is no secret that technolog...
The Risks Your Employees are Taking by Using Public Wi-Fi
Could Your Employees be Accidentally Putting Your Cybersecurity at Risk? Whether...
Which Industries are MOST at Risk for Cyberattacks?
Introduction
Top Cybersecurity Risks Small Businesses Face in 2022
Small Businesses Should Take Steps to Protect Themselves
Cybersecurity Myths that Could be Putting Your Data at Risk
The Importance of Cybersecurity Awareness
How Investing in Managed Cybersecurity Services will Save You Money in the Long Run
Why are Managed Cybersecurity Services so Important?

Most Dangerous Malware Threats in 2022
What Is Malware? Malware, sometimes known as “malicious software,” is a catch-al...
The Risks of Improper Offboarding
Offboarding Incorrectly can Lead to Issues and Security Threats No matter what k...
How to Prevent Internal Threats
How Internal Threats Compromise Businesses, and How To Prevent Them
What You Need to Know About CMMC 2.0
Are you CMMC Compliant?
Pegasus Spyware: The Zero-Click Spyware Infecting Smartphones
Pegasus Spyware: The Basics
The 12 Days of Cybersecurity Christmas
Giving you the Gift of Cybersecurity Awareness this Christmas
A Beginners Guide to Penetration Testing
How Penetration Testing can Improve your Company’s Cybersecurity
Why You need a “Bring Your Own Device” BYOD Policy + Free Template
With the rise of cloud computing, employees have been able to work more efficien...
How a Human Firewall can Increase Your Cybersecurity
The Human Firewall
Improving Productivity with Cloud Services
Cloud Services: A Game-Changer? A huge goal of any company is to improve product...
HIPAA Compliance: What Your Company Needs To Know
The basics you should know before the audit
Replace Your Antivirus with Next-Generation Endpoint Security
Endpoint Security: The Cutting Edge of Protection
How Cyber Liability Insurance Can Protect Your Company From Disaster
Everything You Need To Know About Cyber Liability Insurance
The Savvy Business Owner’s Guide to Cybersecurity Consulting
Everything you need to know about Cybersecurity Consulting Services
Single Sign-On: A Comprehensive Guide
What Is Single Sign-On Authentication & How Does It Work?
Why Data Hygiene Matters
Cleaning Up with Data Hygiene Data hygiene often gets lost in the shuffle. After...
10 Ways Data Loss Prevention Benefits Your Company
This article was originally published September 2021. Updated April 2024. What i...
Everything You Need To Know About PCI Compliance For Your Business
PCI Compliance Doesn’t Need to Be an Impossible Task For the longest time, busin...
3 Ways Software Updates Can Increase Cybersecurity
A Simple Step in Cyber-Attack Prevention Cybersecurity is often a complex undert...
The Future of Passwords and Password Management
The Best Password Managers to Keep You Protected Passwords have been around for ...
Understanding PrintNightmare: a Print Spooler Vulnerability
PrintNightmare: Understand and Overcome
5 Ways to Make Cloud Computing Work for You
For many, “the cloud” is a familiar term, although many struggle to describe wha...
Social Engineering: Common Methods, Examples, and Preventative Measures
What is Social Engineering? Social engineering is a strategy that has invaded mu...
Optimize Microsoft 365 For Better Security Without Spending A Dime
Microsoft Office has been around since 1990 & is here to stay. The newest pr...
Phishing 101: A Beginner’s Guide to Today’s Biggest Cybersecurity Threat
In today’s world, email is one of the most used means of communication. In fact,...
Security Measures to Consider as Employees Return to the Office
Best Cybersecurity Practices for Your Employees as They Return to the Office dur...
6 Ransomware Trends All Employees Should Watch For in 2021
Ransomware is an ever-present and worsening problem in today’s society. It’s cru...
10 Ways To Prevent A Security Breach In The Workplace
Among all the challenges businesses are facing today, cybersecurity is perhaps t...
Centennial School District Compromised by Ransomware
On the News: Edge Networks Discusses the Centennial School District Cyber Attack...
How to Maintain the Cybersecurity of Your Remote Workers
The Sudden Jump to Remote Work: The Need For the Cybersecurity of Your Remote Wo...
8 Good Cyber Hygiene Tactics to Keep Your IT Humming
Keep Your IT Humming with These Cyber Hygiene Tactics Maintaining a healthy and ...
Data Loss Prevention: How to Protect Your Data When Disaster Strikes
Data Loss Prevention: Preparing for a Rainy Day One of the most terrifying exper...
Breaking Down the Cloud: Picking the Right Cloud Management Platform
Aim for the Sky with Application and Cloud Management Over the past decade, we h...
The Role of Employee Security in Building a Secure & Stable Business Environment
Employee Security Matters: The First Line of Cyber Security Defense When conside...

4 Things You Need to Consider When Creating an Effective Device and Inventory Management System
Understanding Device and Inventory Management Business process improvement guru,...

Compliance Mistakes You Don’t Know You’re Making That Can Cost You Thousands
Taking the Fear of Compliance Mistakes out of Regulatory Compliance The phrase “...
The Five Critical Components Your Cybersecurity Incident Response Plan Must Have
What Is a Cyber Incident Response Plan? According to the National Institute of S...
Make Cybersecurity Part of Your Onboarding and Offboarding
Importance of Cybersecurity in the Employee Onboarding and Offboarding Process M...
How Do I Create a Security Awareness Program – Employee Security Awareness Training
Reducing threats better than a firewall, intrusion detection system, or endpoint...

Top 3 Tips for Rock-Solid Microsoft Office 365 Security
Microsoft Office 365 Security – Best Practices Microsoft Office 365 is among the...

Boosting Productivity and Security with Single Sign-On Authentication
Save Time and Hassle with Single Sign-On Authentication (SSO)

Don’t Be the Next Company Sending Out a Notice of Data Breach Letter
Don’t Be the Next Company Sending Out a Notice of Data Breach Letter
Bulk configure handheld scanners Intermec CK3 via CloneNGo
Josh McKinney, chief technology officer with Edge Networks with a tip of the wee...
Stay ahead with edgefi insights
Explore expert articles, guides, and resources to keep your business secure, efficient, and innovative. Discover actionable strategies today.



.png?width=400&height=219&name=guidance%20from%20experts%20(4).png)
