Cybersecurity: What Is It And Why It’s Important For Your Small Business
In the past year, the cost of data breaches in the United States rose 10 percent to reach an all-time high of $4.24 million. In today’s technological business world, the importance of cybersecurity can’t be overestimated. Cybersecurity is essential for small and medium business owners. Think about how much your business relies on technology. How much of your company’s data gets stored on computers, personal devices, and other systems?
Digital business networks are practically universal. At the same time, cybercriminals are growing more innovative by the day. A data breach can be especially devastating for small business owners. There is no way to guarantee these things won’t happen to your business, but there are many precautions you can take to minimize your risk. Keep reading to find out what steps you can take to improve cybersecurity for your small business.
What is Cybersecurity?
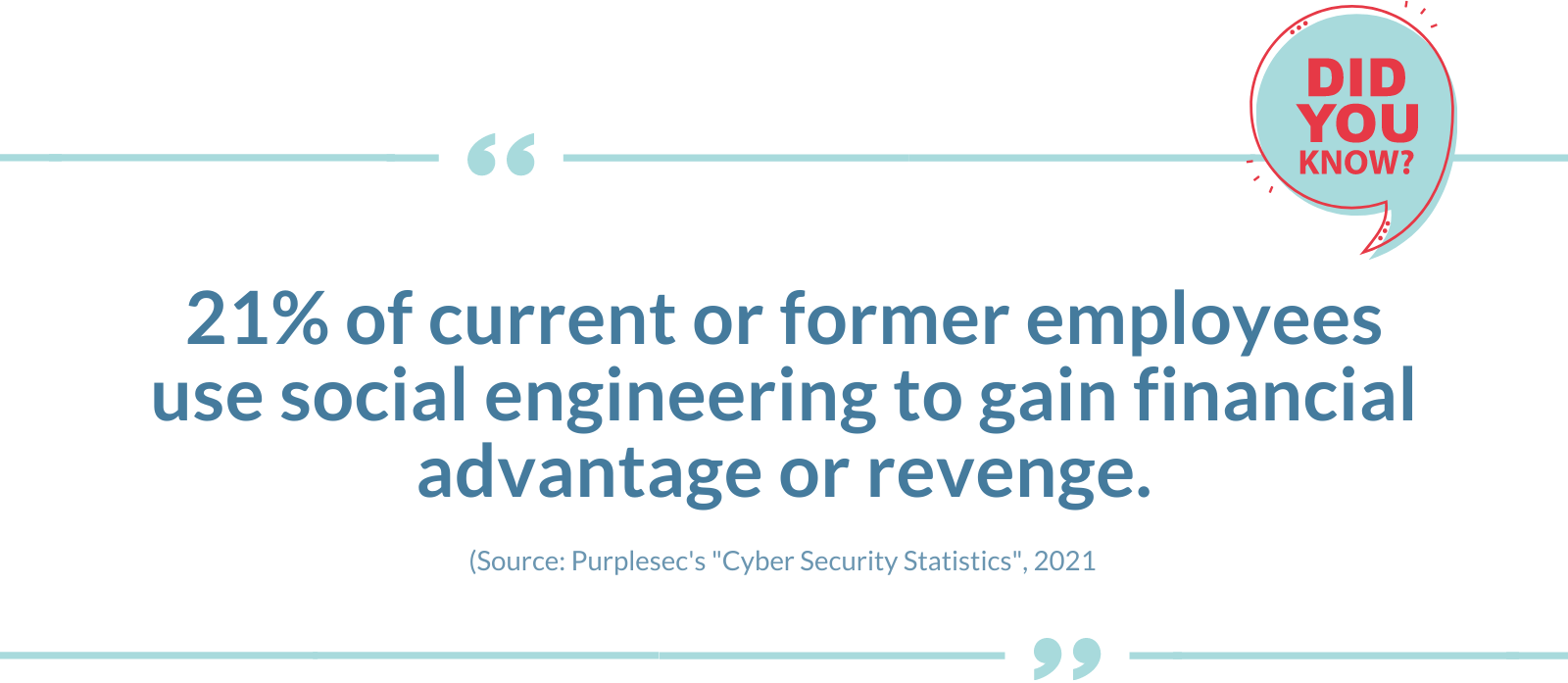
Cybersecurity is the practice of fortifying digital networks, devices, and data against attacks. But the cybersecurity definition goes further than that. The art of cybersecurity involves taking enhanced measures to combat any threat to your network security whether that threat comes from an external organization or inside your own company. Cybersecurity ensures integrity and confidentiality. It limits the availability of sensitive information and prevents unauthorized access.
What Are the Risks of Weak Cybersecurity?
The risks of weak cybersecurity vary in severity. There is the possibility of a malware attack that could erase the contents of your entire system. Similarly, hackers could break into your system to change or alter data and information. A cybercriminal could also use your business’s system to attack others. They could steal your financial information. They could even use your business accounts to make unauthorized purchases.
Cybercriminals target personally identifiable information (PII). This includes names, addresses, social security numbers, bank accounts, and credit card information. Once they have this information, they can sell it in underground digital markets. When your business’s PII gets compromised, it can lead to major problems. Customers may lose trust in your business. You could be forced to pay regulatory fines and even face legal action.
If you have a complex system but lack IT experience managing it, the cost of a data breach could be even higher for your SMB. Small and medium business owners with comprehensive cybersecurity strategies are better protected. They can minimize the frequency and impact of cybersecurity breaches.
What Are the Essential Domains of Effective Cybersecurity?
The more layers there are to your cybersecurity strategy, the better your system gets protected. Here are some of the countermeasures an effective cybersecurity strategy should include.
Critical Infrastructure Security
Your SMB needs critical infrastructure security to protect its systems, networks, and assets. The National Institute of Standards and Technology (NIST) has a cybersecurity organizational framework.
Network Security
Network security refers to measures taken to protect computer networks from cyber attacks. This security applies to both wired and wireless network connections.
Application Security
Application security processes protect the apps your business operates on-site or in the cloud. Incorporating this type of security during the application design stage is vital. That’s when you can take data handling and user authentication into consideration.
Cloud Security
It is important to use encryption data to protect the information your company stores in the cloud. This supports customer privacy and compliance standards. It encrypts all types of cloud data, whether at rest, in motion, or in use.
End-User Education
Cybersecurity training is essential across an organization. Promoting security awareness among employees strengthens cybersecurity.
Disaster Recovery & Business Continuity
When an unplanned event does occur, it is important to have procedures for handling and minimizing the impact. This planning will enable your business to continue as usual despite a power outage, natural disaster, or cyber attack.
Benefits of Cybersecurity for Small Business Owners
Cybersecurity management services use a combination of these domains and more. For this reason, the benefits of cybersecurity for small business owners are far-ranging. Cybersecurity protects data from getting lost, deleted, or accessed by unauthorized parties. It also prevents financial fraud, embezzlement, and financial loss. Protection from viruses and malware attacks as well. That way, your business’s productivity doesn’t get interrupted by damaged hardware. Cybersecurity also protects your intellectual property and data from exposure. Combined, the benefits of cybersecurity will increase your customer’s confidence in your company.

How To Improve Cybersecurity for Small and Medium Business Owners
Sometimes, the purpose of a cyber attack is to gain access to sensitive information. Sometimes the goal is to change or destroy it. Other times, cybercriminals attack with the intention of interrupting business processes for extortion. Here are some of the steps corporations are taking to strengthen cybersecurity protocols.
Complex Passwords
Using robust and complicated passwords is an essential first step in cybersecurity. It might seem obvious, but over half of internet users recycle passwords between accounts. This makes it exceptionally easy for hackers to access multiple accounts with a single password breach.
When choosing a password, include a variety of letters, numbers, and special characters. It will be more difficult for cybercriminals to hack into your accounts and systems. Always avoid using any easily identifiable information in your passwords. This type of information includes names, dates of birth, addresses, etc. Even more importantly, do not store your passwords in easy-to-access locations.
In offices, it is common to write passwords on post-it notes and stick them in highly visible locations. Avoid doing this as it provides an easy invitation for hackers. Finally, make sure to change your passwords often. This is just one more way you can improve your password security throughout your network.
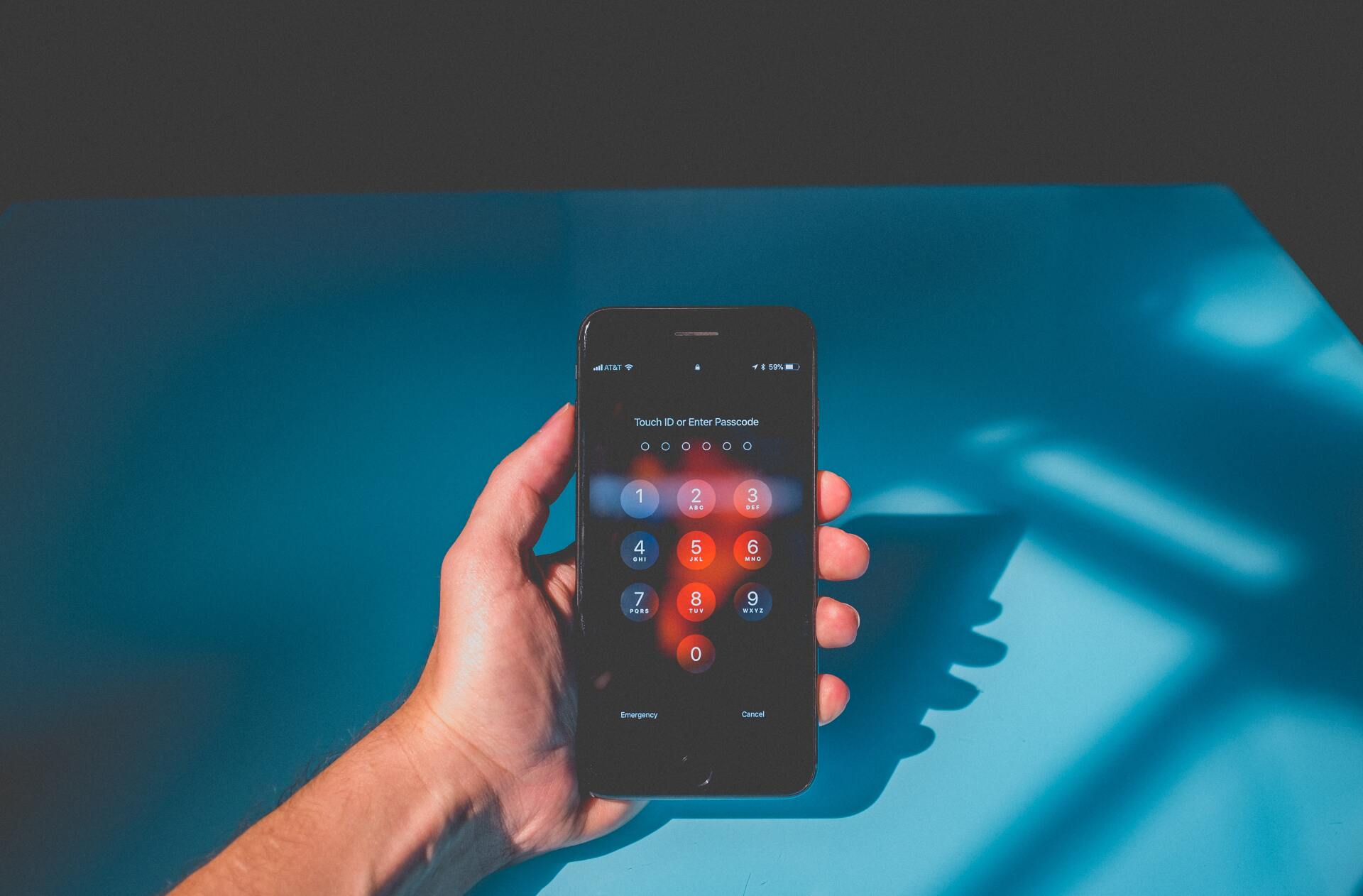
Multi-Factor Authentication
Multifactor authentication (MFA) is an extra layer of security that goes beyond passwords. It is an essential tool all small and medium business owners should use. Instead of relying on passwords alone, multifactor authentication creates an extra access barrier. To get into the account, you will need to provide added proof of your identity.
When you have multifactor authentication, having a password stolen isn’t as big of a deal. It will still be very difficult for an unauthorized entity to get into your account. Multifactor authentication can rely on personal knowledge only the account holder would know. It can also be a physical token like a key fob, mobile phone, or USB device.
The most secure multifactor authentication relies on biometrics. This might include fingerprints, retina scanning, or facial and voice recognition. In addition, MFA alerts users to unauthorized attempts to log into their accounts. That way, you and your IT management team can handle it immediately.
Email Security
The majority of cyberattacks occur via email. Switch to an email program that will limit your exposure to attacks by reducing email spam.
Employee Education
It is essential to educate your employees about the dangers of cyberattacks. Cybersecurity training should be part of every employee’s onboarding process. Many businesses use social media to attract customers. Make sure to inform your employees on how to handle social media posts. That way, they won’t disclose sensitive information to a competing business.
Network Security
Using firewalls and encryption is important for any SMB. It is especially important when working remotely or in public. Say you want to take a working lunch at a coffee shop. Connecting to free wifi can put your data at risk. Invest in a portable hotspot with a secure network instead.
Personal Computer & Device Monitoring
Do your employees use personal devices to do work? Your network administrator should have access to these devices. You don’t need to worry about invading your employees’ privacy. Your network administrator only needs to install security updates and track software.

Back-Up Your Files
Every month, make it a habit to back up all your data. This will prevent the possibility of data loss. Remember to back up your local data and what you have stored in the cloud.
Hire an IT Management Service
None of these precautions alone will completely protect your business. The best way to get comprehensive cybersecurity is to use an IT management service. A cybersecurity analyst will begin by performing a security assessment. This allows them to see how well your current security system is working. They will then make the necessary enhancements to protect your data better.
Cybersecurity Services For Your SMB
Minimizing costs is important to small and medium business owners. But if there is one area where you shouldn’t pinch pennies, it is IT support and cybersecurity. One cyber attack could be enough to destroy your business. As a small business owner, you stand to lose time, money, and the trust of your customers. Find out how Edge Networks can improve cybersecurity for your SMB. Contact us today to learn more.